Introduction
In the world of collectibles, authenticity is everything. Whether you’re a seasoned collector or a novice just starting out, the thrill of acquiring a new piece is often tempered by one crucial question: Is it real? This is where card authentication comes into play, a process that has become increasingly important in the collectibles market.
In this comprehensive guide, we delve into the world of card authentication, exploring its importance for collectors, the science behind it, and the role of third-party services in ensuring the authenticity of your prized possessions. So, buckle up and join us on this journey into the fascinating world of card authentication.
Remember, knowledge is power, and in the world of collecting, it could mean the difference between owning a priceless treasure and falling victim to a clever forgery.
Stay tuned as we unravel the intricacies of card authentication and why it’s a game-changer for collectors worldwide.
What is Card Authentication?
Imagine this: You’ve just acquired a rare baseball card, a gem that you’ve been hunting for years. The excitement is palpable, but so is the nagging doubt. Is it authentic? This is where card authentication comes into the picture.
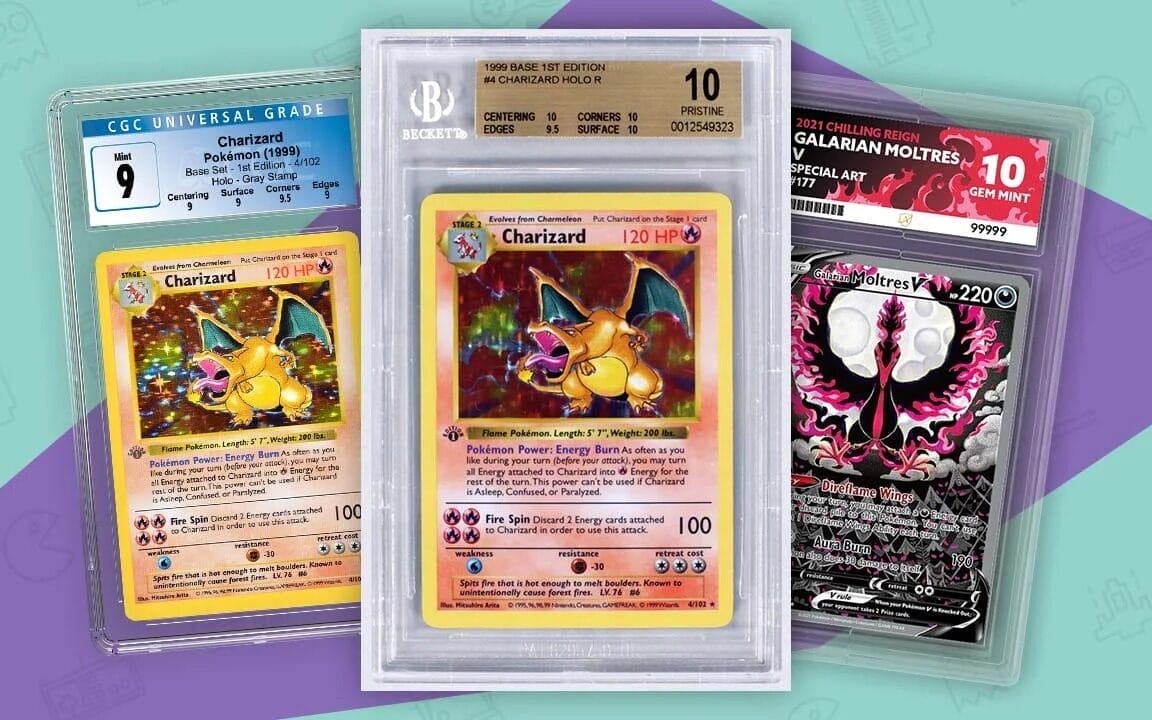
Card authentication is a process that verifies the authenticity of collectible cards. It involves a comprehensive examination of the card, from its physical characteristics to its provenance, to ensure it’s not a forgery or a duplicate.
In the world of collectibles, the authenticity of a card can significantly impact its value. A card that has been authenticated by a reputable third-party service can fetch a higher price in the market compared to an unauthenticated card.
But how does this process work? And who are these third-party services that hold the power to authenticate these cards? Let’s dive deeper into the world of card authentication to find out.
Benefits of Third-Party Authentication

When it comes to the world of card collectibles, third-party authentication services offer a range of benefits that are invaluable to both collectors and sellers. Let’s explore some of the key advantages of utilizing these services:
Establishing Trust and Confidence
Trust is the foundation of any successful marketplace, and third-party authentication services play a vital role in establishing trust and confidence among collectors. By having a reputable third-party authenticate a collectible card, buyers can be assured that they are purchasing a genuine and valuable item. This assurance not only protects buyers from falling victim to forgeries but also gives them the confidence to invest in high-value cards.
Ensuring Accurate Grading
In addition to verifying authenticity, third-party authentication services also provide grading for collectible cards. Grading involves assessing the condition and quality of the card, assigning it a grade that reflects its overall state. This grading system helps collectors and sellers accurately determine the value of their cards and ensures fair transactions in the marketplace.
Increasing Market Value
Cards that have been authenticated by trusted third-party services often command a higher market value compared to unauthenticated cards. The authentication process adds credibility and legitimacy to the card, making it more desirable to collectors. As a result, authenticated cards can fetch premium prices in the market, benefiting both sellers and collectors.
Expertise and Industry Standards
Third-party authentication services, such as Professional Sports Authenticator (PSA) and Beckett Grading Services (BGS), have established themselves as industry leaders in card authentication. These organizations have a team of experts with extensive knowledge and experience in examining and grading collectible cards.
However, trading card grading has long been a contentious issue within the collector community, with concerns frequently raised about its subjectivity, inconsistency, and potential biases. These challenges have sometimes led to disputes and uncertainties among collectors and traders, undermining the very purpose of grading – to provide clarity and assurance.
Recognizing these issues, our company, Special One Cards, has chosen a distinct path. Instead of delving into the subjective realm of grading, we focus solely on authentication. By ensuring the genuineness of a card without assigning a grade, we aim to offer collectors a trustworthy service that eliminates the ambiguities and controversies associated with grading.
Protection Against Forgeries
One of the biggest challenges in the world of card collectibles is the presence of forgeries. Counterfeit cards can be incredibly convincing, making it difficult for collectors to differentiate between genuine and fake items. Third-party authentication services employ advanced techniques and expertise to identify forgeries, protecting collectors from purchasing counterfeit cards.
By utilizing third-party authentication services, collectors can have peace of mind knowing that their cards are genuine, accurately graded, and protected against forgeries. These services not only enhance the overall experience of collecting but also contribute to the growth and integrity of the card collectibles market.
The Science of Card Authentication
In the world of credit cards, authentication plays a crucial role in ensuring the security of transactions and protecting against fraud. Let’s delve into the science behind card authentication and explore the different methods used to verify the identity of cardholders.
Understanding Credit Card Authentication
Credit card authentication is the process of confirming the identity of a person attempting to use a credit card for a transaction and ensuring that they are authorized to use the card. It is an essential tool in the fight against credit card fraud. Authentication is distinct from authorization, which verifies additional information such as the availability of sufficient credit to cover the transaction.
Methods of Credit Card Authentication
There are several methods used to authenticate credit card transactions, depending on whether they are card-present or card-not-present transactions:
Card-Present Transactions
In card-present transactions, where the physical card is present at the point of sale, authentication methods may include:
- Signature or PIN: The merchant may require the cardholder to provide a signature or enter a PIN during the transaction.
- Driver’s License or ID: The merchant may request to see a driver’s license or another form of identification to verify the cardholder’s identity.
Card-Not-Present Transactions
In card-not-present transactions, where the cardholder is not physically present, authentication methods may include:
- CVV or CID: The customer may be asked to provide the Card Verification Value (CVV) or Card Identification (CID) number. CVV is typically a three-digit number found on the back of the card, while CID is a four-digit number found on the front.
- Multi-Factor Authentication: Online and mobile transactions often require additional authentication measures, such as multi-factor authentication, to enhance security. This may involve the use of one-time codes sent to the customer’s mobile phone or email.
Biometric Authentication
Biometric authentication is an advanced form of credit card authentication that uses unique physical or behavioral characteristics to verify a cardholder’s identity. Biometric information such as voice or facial recognition, iris or retinal scans, or fingerprint identification can be used for authentication purposes. This technology offers increased efficiency and security compared to other authentication methods.
Importance of Security in Card Authentication
As technology evolves, so do the methods used for card authentication. With the introduction of contactless smart cards and match-on-card technologies, additional security measures are necessary to ensure the encryption and secure transmission of transaction data. Organizations like NIST (National Institute of Standards and Technology) conduct studies to explore advancements in smart card technology and the impact of security on performance.
By understanding the science behind card authentication and implementing secure authentication methods, businesses can protect themselves and their customers from credit card fraud, ensuring safe and reliable transactions.
The Future of Card Authentication
As technology continues to advance, the future of card authentication holds exciting possibilities. Innovations in authentication methods and technologies are shaping the way we secure our credit cards and protect against fraud. Let’s explore some of the emerging trends and advancements in card authentication:
Biometric Authentication
Biometric authentication is gaining traction as a secure and convenient method of card authentication. With the use of unique physical or behavioral characteristics such as fingerprints, facial recognition, or iris scans, biometric authentication offers a high level of security and eliminates the need for passwords or PINs. As biometric technology becomes more accessible and reliable, we can expect to see wider adoption in the authentication process.
Tokenization
Tokenization is another promising trend in card authentication. It involves replacing sensitive card information, such as the card number, with a unique identifier or token. This token is used for transactions, reducing the risk of exposing sensitive data. Tokenization adds an extra layer of security and makes it more challenging for hackers to intercept and misuse card information.
Mobile Wallets and Contactless Payments
The rise of mobile wallets and contactless payments is transforming the way we make transactions. With mobile wallets like Apple Pay, Google Pay, and Samsung Pay, users can securely store their card information on their smartphones and make payments by simply tapping their devices. These mobile wallets utilize various authentication methods, such as fingerprint or facial recognition, to ensure secure transactions.
Blockchain Technology
Blockchain technology, known for its decentralized and secure nature, has the potential to revolutionize card authentication. By leveraging blockchain, card transactions can be recorded in a transparent and tamper-proof manner, reducing the risk of fraud. Blockchain-based authentication systems can provide a higher level of trust and security, ensuring the integrity of card transactions.
Artificial Intelligence and Machine Learning
Artificial intelligence (AI) and machine learning (ML) are playing an increasingly important role in card authentication. These technologies can analyze vast amounts of data and detect patterns or anomalies that may indicate fraudulent activity. AI-powered authentication systems can continuously learn and adapt to new threats, enhancing the security of card transactions.
As the landscape of card authentication continues to evolve, these emerging trends and advancements hold great promise for a more secure and convenient future. By embracing new technologies and staying vigilant against evolving threats, we can ensure the integrity and safety of our card transactions.
Best Practices for Implementing Third-Party Authentication in E-commerce
Implementing third-party authentication in your e-commerce platform can bring numerous benefits, but it’s essential to follow best practices to ensure a smooth and secure integration. Let’s explore some key considerations and best practices for implementing third-party authentication:
Choose a Reliable and Trusted Provider
When selecting a third-party authentication provider, it’s crucial to choose a reliable and trusted service. Look for providers with a proven track record in the industry and positive reviews from other businesses. Consider factors such as security measures, uptime, customer support, and scalability to ensure a seamless integration and a reliable authentication experience for your users.
Understand the Authentication Flow
Before integrating a third-party authentication service, take the time to understand the authentication flow and how it will fit into your e-commerce platform. Familiarize yourself with the APIs, SDKs, or plugins provided by the authentication service and ensure they align with your technical requirements. This understanding will help you plan and implement the integration effectively.
Implement Secure Communication
Ensure that all communication between your e-commerce platform and the third-party authentication service is secure. Use secure protocols such as HTTPS to encrypt data transmission and protect sensitive information. Regularly update and patch your server and software to address any security vulnerabilities and stay up-to-date with the latest security practices.
Customize the User Experience
While leveraging a third-party authentication service, it’s essential to customize the user experience to align with your brand and platform. Customize the login and registration screens to match your website’s design and branding. Provide clear instructions and guidance to users during the authentication process to ensure a seamless and intuitive experience.
Regularly Monitor and Test
Once the third-party authentication integration is in place, it’s crucial to regularly monitor and test the authentication system. Monitor for any unusual activity or suspicious login attempts and promptly address any security concerns. Conduct regular penetration testing and vulnerability assessments to identify and mitigate potential risks.
Provide Clear Privacy Policies
Transparency and privacy are paramount when implementing third-party authentication. Clearly communicate to your users how their data will be used, stored, and protected. Provide a comprehensive privacy policy that outlines your data handling practices and compliance with relevant regulations such as GDPR or CCPA. This transparency builds trust and reassures users about the security of their information.
By following these best practices, you can ensure a secure and seamless integration of third-party authentication into your e-commerce platform. By choosing a reliable provider, understanding the authentication flow, implementing secure communication, customizing the user experience, regularly monitoring and testing, and providing clear privacy policies, you can enhance the security and user experience of your e-commerce platform.
Conclusion: Securing the Future of Card Authentication

In today’s digital age, the importance of card authentication cannot be overstated. As we rely more on credit cards for our financial transactions, it becomes crucial to implement robust authentication methods to protect against fraud and unauthorized access. Through this blog post, we have explored the significance of card authentication and the various methods and technologies that are shaping its future.
From the traditional methods of PINs and passwords to the emerging trends of biometric authentication, tokenization, mobile wallets, blockchain technology, and artificial intelligence, the landscape of card authentication is constantly evolving. These advancements not only enhance security but also provide a more convenient and seamless user experience.
By implementing biometric authentication, users can enjoy the convenience of using their unique physical or behavioral characteristics to authenticate transactions. Tokenization replaces sensitive card information with unique identifiers, reducing the risk of data exposure. Mobile wallets and contactless payments revolutionize the way we make transactions, leveraging authentication methods such as fingerprint or facial recognition. Blockchain technology ensures transparent and tamper-proof card transactions, while artificial intelligence and machine learning analyze data to detect and prevent fraudulent activity.
As we move forward, it is crucial for businesses and individuals to stay updated with the latest authentication methods and technologies. By embracing these advancements and implementing best practices, we can secure the future of card authentication and protect ourselves against evolving threats.
In conclusion, card authentication is a vital aspect of our digital lives. By understanding the importance of authentication methods, staying informed about emerging trends, and implementing secure and convenient authentication practices, we can ensure the integrity and safety of our card transactions. Let us embrace the future of card authentication and pave the way for a secure and seamless financial landscape.